CMMC: New Security Standards for DoD Contracts

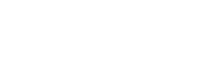
CMMC or Cybersecurity Maturity Model Certification is created and managed by the DoD. The CMMC framework is comprised of five processes and 171 cybersecurity best practices that advance through five maturity levels. The goal of the maturity process is to institutionalize cyber security activities and ensure they are consistent, repeatable and high quality. The CMMC framework is paired with a certification program that verifies the implementation of processes and practices with those working with and for the DoD.
Five levels of CMMC
The processes range from “performed” at Level 1 to “Optimizing” at level 5 and the practices range from “Basic Cyber Hygiene” at Level 1 to “Advanced/Progressive” at Level 5.
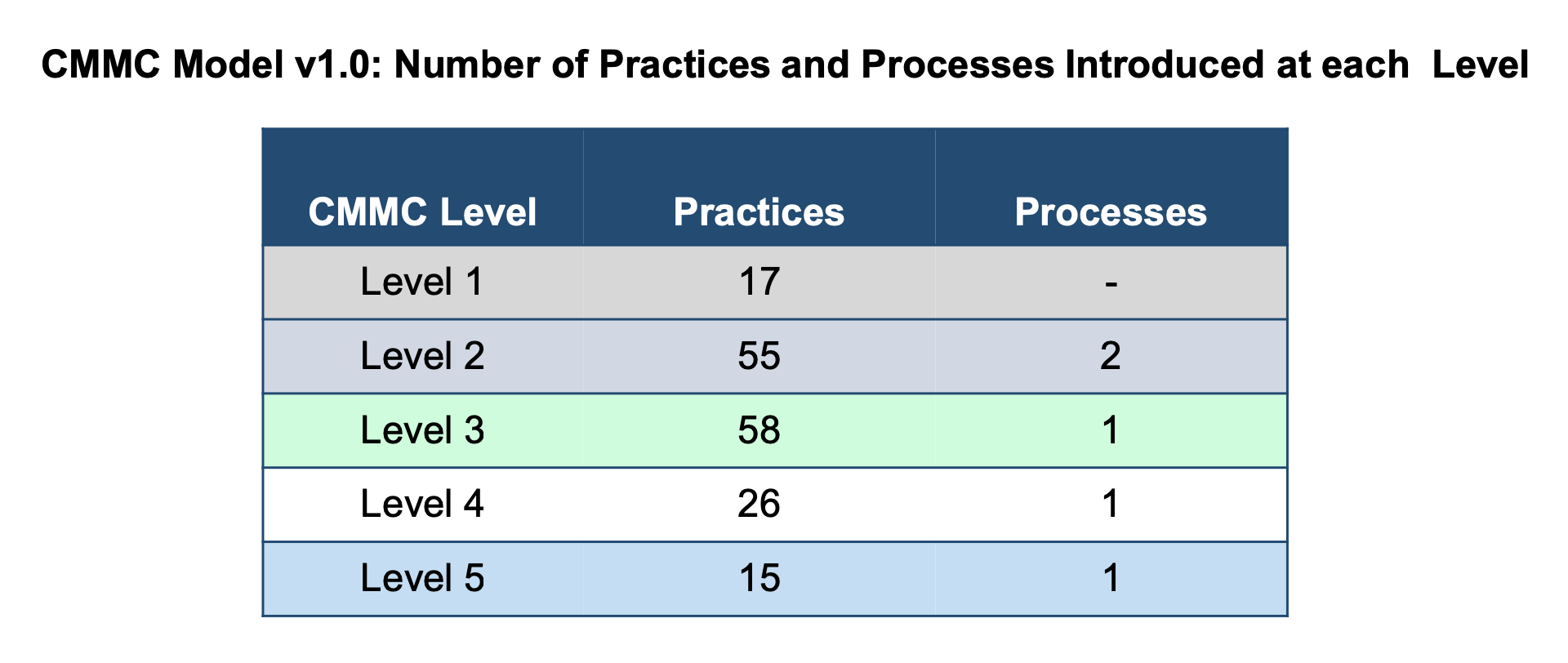
LEVEL 1
This level is comprised of basic cyber hygiene practices and performed processes. The focus of level one is to safeguard federal contract information (FCI). Level 1 requires one to perform specific practices, 17 to be exact. It focuses on the protection of FCI and the practices correspond to basic safeguarding. See more about required practices and why in the full PDF.
LEVEL 2
This process requires documentation and is referred to as intermediate cyber hygiene. It requires a business to establish and document practices and policies while implementing CMMC efforts. Documentation of their efforts ensures one can do them repeatedly and implementing consistent practice of them. Level 2 is an intermediary from level 1 to 3 allowing for a smooth progression. Due to level 2 being a transitional phase, the practices reference the protection of CUI and must comply with FAR. Review Level 2 further
LEVEL 3
Once a company has reached Level 3, they are considered having good cyber hygiene. Level three has 130 practices to follow. You must comply with FAR, encompass all practices from NIST SP 800-171 r1 and includes an additional 20 practices that support good cyber hygiene. This level states a company must establish, maintain and resource a plan demonstrating the management of activities for practice implementation. A plan can include missions, goals, project plans, etc. The focus of level 3 is to protect CUI.
LEVEL 4
Level four requires an organization to review and measure practices for effectiveness and to be proactive in the protection of CUI from APTs [advanced persistent threat] and includes a subset of enhanced security requirements from Draft NIST SP 800-171B [6]. Level 4 includes 156 practices, including 15 set out specifically for a proactive cybersecurity program. The practices enhance the detection and response capabilities of an organization to address and adapt to changing tactics, techniques, and procedures [TTPs] used by APTs.
LEVEL 5
To obtain level 5 in CMMC, an organization must be considered advanced and progressive. One must comply with 171 practices, FAR, and include an additional 11 practices to demonstrate an advanced cybersecurity program. By level 5, an organization must have a standardized and optimized process implementation across all departments. Like Level 3 and 4, Level 5’s focus is on protection of CUI from APTs but with additional practices to increase depth and sophistication of cybersecurity capabilities.
Here is an overview of what has been covered. Discover more information in the official DoD PDF.
The CMMC model contains 17 domains, each with a list of capabilities. The following include:
- Access Control (AC)
- Asset Management (AM)
- Audit and Accountability (AU)
- Awareness and Training (AT)
- Configuration Management (CM)
- Identification and Authentication (IA)
- Incident Response (IR)
- Maintenance (MA)
- Media Protection (MP)
- Personnel Security (PS)
- Physical Protection (PE)
- Recovery (RE)
- Risk Management (RM)
- Security Assessment (CA)
- Situational Awareness (SA)
- System and Communications Protection (SC)
- System and Information Integrity (SI)
For a full overview of what capabilities are included in each domain, visit the diagram in the full PDF.
This blog gives a very broad overview of what is entailed in the CMMC model. The JFG team is here to answer questions you may have and to help your organization reach the level of compliance required for work specific to you.